There is no great application without a great security architecture. You don't build business solutions without protecting your business logic. Imagine a thriving business, with clients everywhere in the global village.

In a flip second (unlike the proverbial thief in the night), something happens in broad daylight. Your client data is stolen, key business secrets that were your competitive advantage have become available to your competitors, and your money (investors’ money) is gone to God knows where, ‘sope otilo, iz gone’.
The monetary losses incurred due to security hacks in recent years have been substantial. Organizations often invest significant resources in mitigating security risks and minimizing financial losses through various measures such as cybersecurity protocols, insurance, and incident response strategies.
Security is an essential aspect of every application, and in the realm of enterprise applications, Java holds a prominent position, with Spring Security widely recognized as the go-to solution for robust protection and defense.
Why Spring Security?
Of course, it is Industry Standard😎. Spring Security has established itself as a widely adopted and trusted security framework in the Java ecosystem. Many organizations rely on Spring Security to secure their enterprise applications, making it a valuable skill for developers in the job market.
It is highly flexible and customizable💪. This enables the implementation of complex security scenarios and the ability to adapt to evolving security needs. Developers can tailor security configurations to the specific requirements of the applications being built.
Spring Security offers robust security features that are truly comprehensive. These include authentication, authorization, and session management.
Spring Security seamlessly integrates with other Spring projects, such as Spring Framework, Spring MVC, and Spring Boot. This integration allows developers to leverage the benefits of a cohesive ecosystem.
Worthy mentions include extensive integration with various third-party security solutions, such as OAuth; extensive community support, and documentation.
Having highlighted the numerous advantages of Spring security, it is important to acknowledge a few potential drawbacks:
The learning curve is quite steep📚: Firstly, spring security is a comprehensive framework; sometimes it seems like there are so many moving pieces, and keeping track of it can be quite challenging for beginners. Secondly, Spring Security is a dynamic framework, this means periodic updates and release of new versions. Essentially, the learning process doesn’t end as you have to keep up with the latest updates, bug fixes, and security patches; much effort and attention are required to ensure the application remains secure and up to date.
Challenges with customization: While Spring Security offers extensive customization options, implementing highly specialized or complex security requirements may require additional effort. Understanding and leveraging advanced customization features might require in-depth knowledge of the framework and security concepts.
With dedication, practice, and a solid understanding of security principles, developers can effectively leverage Spring Security to build secure and resilient applications.
The Good News is with Spring boot 3 and Spring Security 6, there is more structure to the previously perceived disorderliness associated with managing dependencies.
Newer updates in the Spring security framework have in my opinion smoothened the hitherto steep learning curve. I like to think there’s a context to things (spring security inclusive) and learning spring security can be enthralling.
This means you only need to understand the moving pieces, in other words, the key players involved in the process. It’s also great news because of the sequential process of learning.
We begin with the starter, literally.
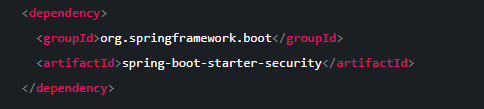
The Spring Boot Starter Security dependency begins our journey into this immersive learning experience.
Afterward, we will begin to navigate certain concepts like basic authentication, in-memory user, database authentication, and JWT implementation.
The good news is, we will approach this step by step and we will arrive at a full understanding of Spring security.
Shall we begin?